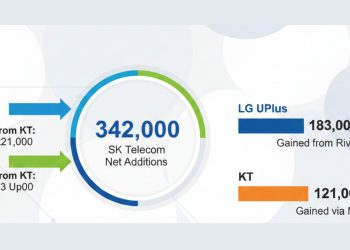
SK Telecom, South Korea’s largest mobile operator, has warned that a malware attack led to unauthorized access to its customers’ sensitive USIM (universal subscriber identity module) information. With about 48.4% of the country’s mobile service market and 34 million subscribers, the company reported the breach to authorities and is investigating the extent of the exposure.
The cyberattack occurred late on April 19, 2025, and was officially confirmed by SK Telecom on April 22. The leak has sparked concerns over potential SIM swapping attacks, drawing comparisons to the 2021 T-Mobile data breach in the United States, where stolen customer data fueled a wave of such incidents.
SK Telecom detected signs of malicious code on its USIM-related systems during a weekend when staffing levels were lower. Upon discovery, the company quickly removed the malware and isolated the affected equipment to prevent further damage. The breach was reported to the Korea Internet & Security Agency (KISA) the next day and to the Personal Information Protection Commission (PIPC) on April 22.
At this stage, SK Telecom says there is no evidence that the compromised USIM data has been misused. However, investigations are still ongoing to determine the full cause and scale of the incident. Authorities, including the Ministry of Science and ICT, are expected to carry out an on-site inspection at SK Telecom’s headquarters in central Seoul. The company emphasized it is working closely with the relevant agencies to support the investigation.
The leaked USIM information typically includes data such as International Mobile Subscriber Identity (IMSI), Mobile Station ISDN Number (MSISDN), and authentication keys. It does not contain sensitive personal details like resident registration numbers or payment information. Still, security experts warn that exposed USIM data could enable targeted surveillance, tracking, and SIM-swapping attacks if abused.
SIM swapping is a growing threat where attackers duplicate a victim’s SIM card to hijack their phone number and intercept authentication codes, often leading to financial theft. In South Korea, around 40 cases of suspected SIM swapping were reported in 2022, with victims losing virtual assets worth up to 270 million won (approximately $192,000). Although these past incidents involved another carrier, KT, the risks highlight the seriousness of USIM data leaks.
SK Telecom has strengthened measures to block unauthorized USIM swaps and detect abnormal authentication attempts to minimize risks following the breach. The company has assured customers that accounts showing suspicious activities will face immediate service suspension to prevent possible misuse.
SK Telecom is advising subscribers to enroll in its USIM protection service through a dedicated portal. This service helps prevent their mobile numbers from being transferred to another SIM without consent. So far, no hacker groups have claimed responsibility for the company’s cyberattack.
The telecom giant has not yet revealed how many users were affected, stating that a full forensic investigation is ongoing. “Due to the nature of cyberattacks, it is difficult to quickly assess the complete scope of the leak,” the company explained, promising to release more information as the joint investigation advances. The growing threat of SIM swapping remains a concern globally, with the FBI reporting $48 million in losses from such attacks in the United States alone in 2023 across roughly 800 reported cases.